Mitigating Security Threats in IoT Networks Using Big Data Analytics and On-Device Modeling
DOI:
https://doi.org/10.5281/zenodo.15037481Keywords:
Secure IOT Infra, Big-Data Analytics, Anomaly Behavior Profiling, Collaborative IOT Security Model, Device Analytics, Secure Model for IOTAbstract
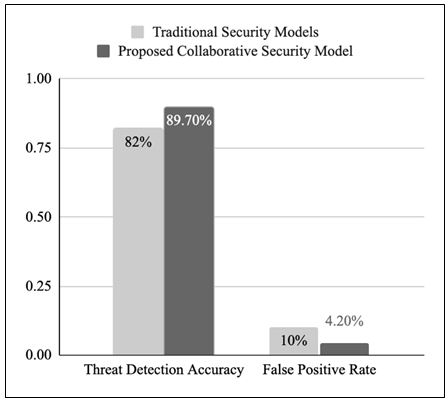
The rapid increase of IoT devices created the modern digital infrastructures but it has also added crucial security challenges due to the scale and heterogeneity of IOT devices. This paper presents a collaborative security framework model that uses big-data analytics & Hybrid on-device modelling that allows us to address the security threats appearing in an IoT ecosystem. The framework uses big data analytics to process huge amounts of IoT traffic data in real time, recognizing patterns, detect possible threats and creates a miniature model that can be deployed on IOT device. On-device modeling helps to ensure that threats can be handled right there on-device, limiting cloud-based infra and latency dependencies. The framework also focus on using an AHD Model (Anomaly Hash-out Delta) using device behavior profile for permissible actions, which helps anomaly handling in a very lightweight machine learning model.
Downloads
References
A. Al-Fuqaha, M. Guizani, M. Mohammadi, M. Aledhari, & M. Ayyash. (2015). Internet of Things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surveys & Tutorials, 17(4), 2347–2376. DOI: 10.1109/COMST.2015.2444095.
L. Atzori, A. Iera, & G. Morabito. (2010). The internet of things: A survey. Comput. Netw., 54(15), 2787–2805. DOI: 10.1016/j.comnet.2010.05.010.
M. Antonakakis et al. (2017). Understanding the mirai botnet. In Proc. 26th USENIX Security Symp., pp. 1093–1110. Available at: https://www.usenix.org/conference/usenixsecurity17/technical-sessions/presentation/antonakakis.
S. Sicari, A. Rizzardi, L. A. Grieco, & A. Coen-Porisini. (2015). Security, privacy and trust in internet of things: The road ahead. Comput. Netw., 76, 146–164. DOI: 10.1016/j.comnet.2015.02.016.
A. Alrawais, A. Alhothaily, C. Hu, & X. Cheng. (2017). Fog computing for the internet of things: Security and privacy issues. IEEE Internet Comput., 21(2), 34–42. DOI: 10.1109/MIC.2017.37.
Y. Meidan et al. (2018). N-BaIoT: Network-based detection of IoT botnet attacks using deep autoencoders. IEEE Pervasive Comput., 17(3), 12–22. DOI: 10.1109/MPRV.2018.03367731.
M. A. Ferrag, L. Maglaras, A. Argyriou, D. Kosmanos, & H. Janicke. (2018). Security for 4G and 5G cellular networks: A survey of existing authentication and privacy-preserving schemes. J. Netw. Comput. Appl., 101, 55–82. DOI: 10.1016/j.jnca.2017.10.017.
F. A. Alaba, M. Othman, I. A. T. Hashem, & F. Alotaibi. (2017). Internet of things security: A survey. J. Netw. Comput. Appl., 88, 10–28. DOI: 10.1016/j.jnca.2017.03.016.
Z. B. Celik, G. Tan, & P. D. McDaniel. (2019). IoT guard: Dynamic enforcement of security and safety policy in commodity IoT. In: Proc. Netw. Distrib. Syst. Security Symp. (NDSS). Available at: https://www.ndss-symposium.org/ndss-paper/iotguard-dynamic-enforcement-of-security-and-safety-policy-in-commodity-iot/.
S. R. Hussain, M. Echeverria, O. Chowdhury, N. Li, & E. Bertino. (2019). Privacy attacks to the 4G and 5G cellular paging protocols using side channel information. In: Proc. Netw. Distrib. Syst. Security Symp. (NDSS). Available at: https://www.ndss-symposium.org/ndss-paper/privacy-attacks-to-the-4g-and-5g-cellular-paging-protocols-using-side-channel-information/.
M. A. Razzaq, S. H. Ahmed, S. A. Hussain, & M. K. Khan. (2017). Security issues in the internet of things (IoT): A comprehensive study. Int. J. Adv. Comput. Sci. Appl. (IJACSA), 8(6), 383–388. Available at: https://thesai.org/Publications/ViewPaper?Volume=8&Issue=6&Code=IJACSA&SerialNo=54.
L. Atzori, A. Iera, & G. Morabito. (2010). The internet of things: A survey. Comput. Netw., 54(15), 2787–2805. DOI: 10.1016/j.comnet.2010.05.010.
M. Elrawy, A. Awad, & H. Hamed. (2018). Intrusion detection systems for IoT-based smart environments: A survey. J. Netw. Comput. Appl., 121, 18–40. DOI: 10.1016/j.jnca.2018.07.016.
L. D. Xu, W. He, & S. Li. (2014). Internet of things in industries: A survey. IEEE Trans. Ind. Informat., 10(4), 2233–2243. DOI: 10.1109/TII.2014.2300753.
J. Lin, W. Yu, N. Zhang, X. Yang, & H. Ge. (2017). A survey on internet of things: Architecture, enabling technologies, security and privacy, and applications. IEEE Internet Things J., 4(5), 1125–1142. DOI: 10.1109/JIOT.2017.2683200.
M. Almiani, A. AbuGhazleh, A. Al-Rahayfeh, S. Atiewi, & A. Razaque. (2020). Deep recurrent neural network for IoT intrusion detection system. Simul. Model. Pract. Theory, 101, 102031. DOI: 10.1016/j.simpat.2019.102031.
S. J. Moore, T. J. Moore, & J. H. Reed. (2020). Reliability of IoT devices: A review. IEEE Internet Things J., 7(4), 2986–2998. DOI: 10.1109/JIOT.2020.2970123.
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 Vinny Sukhija, Dr. Brij Mohan Goel

This work is licensed under a Creative Commons Attribution 4.0 International License.
Research Articles in 'International Journal of Engineering and Management Research' are Open Access articles published under the Creative Commons CC BY License Creative Commons Attribution 4.0 International License http://creativecommons.org/licenses/by/4.0/. This license allows you to share – copy and redistribute the material in any medium or format. Adapt – remix, transform, and build upon the material for any purpose, even commercially.