A Review on Intrusion Detection in Cloud Computing
DOI:
https://doi.org/10.31033/ijemr.13.2.35Keywords:
Cloud based IDS, Intrusion, Anomaly, Soft ComputingAbstract
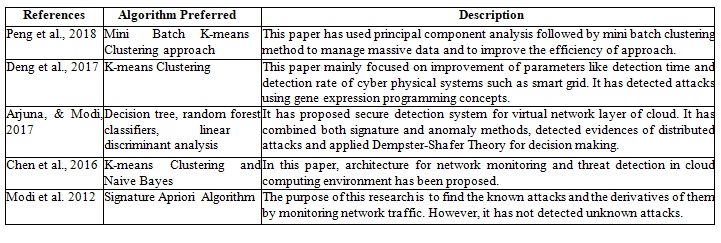
Rapid growth of resources and escalating cost of infrastructure is leading organizations to adopt cloud computing. Cloud computing provides high performance, efficient utilization, and on-demand availability of resources. We propose an intrusion detection system which is based on the cloud computing to reduce the risk of intrusion on the cloud networks and cover up the deficiency of already in use intrusion detection systems. Intrusion Detection System (IDS) in Cloud Computing is a security solution designed to detect and prevent unauthorized access and malicious activity in cloud computing environments. Cloud computing refers to the use of remote servers hosted on the internet to store, manage, and process data instead of using local servers or personal computers .Our design is based on cloud computing Software-as-a service (SaaS) model for detection and prevention of intrusion cloud-based users. Additionally, the study will also address virtual machine introspection (VMI) and hypervisor introspection (HVI) strategies. The current study is organized on the basis of three distinct: cloud security concerns, the importance of feature selection, and the analysis of existing IDS techniques. Finally, this work presents a review of existing security issues/challenges and research gaps for future research. Then, a combined survey of IDS on the basis of signature and anomaly detection approaches is given in another tabular form so as to get a clear analysis about attacks to be detected, advantages and challenges to be faced by existing methods.
Downloads
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Monis Tariq, Mohd. Suaib

This work is licensed under a Creative Commons Attribution 4.0 International License.