Secure Authentication and Key Management Protocol in Cloud Computing
DOI:
https://doi.org/10.31033/ijemr.13.3.25Keywords:
Cloud Computing, Security Issues, Authentication, Authorization, Encryption, Key ManagementAbstract
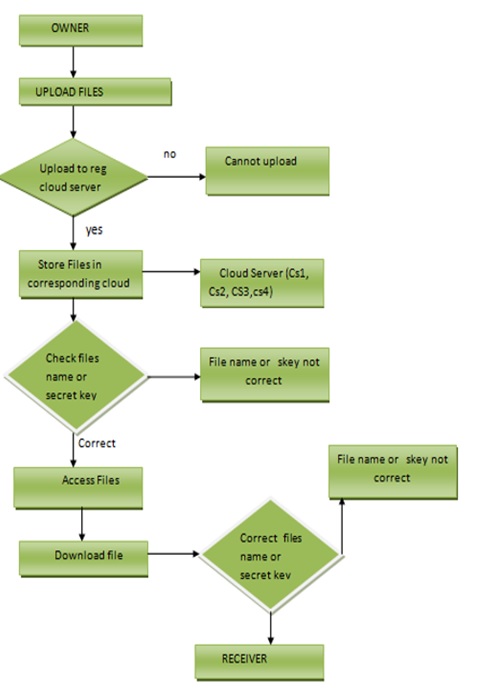
Cloud computing has brought revolution in IT (Information Technology) sector. It has transform the way organizations and individuals process, store and access applications and data , by offering scalable and on-demand access to computing resources including networks, servers, storage and applications. It is a flexible service that allows users to dynamically scale up and down their resources based on demand which enhances efficiency and optimizes resource utilization .Cloud computing offers number of benefits and saves cost. It eliminates the need for investing in hardware and software. Cloud computing allows users to work from anywhere over internet connection which enhances productivity .However, cloud computing has some challenges such as Security concerns that include unauthorized access and data breach. To provide security in cloud computing environment various authentication and authorization protocols exist but they also suffers from various security attacks. Nowadays three factor MAKA (Mutual Authentication and Key Management) protocol has gained popularity but they also lacked as they don’t have dynamic revocation mechanism .To address these issues we have proposed a system based on id , password and biometric based authentication that has dynamic revocation mechanism and can resist various known attacks.
Downloads
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Umaima Fatima, Dr. Sheeba Parveen

This work is licensed under a Creative Commons Attribution 4.0 International License.